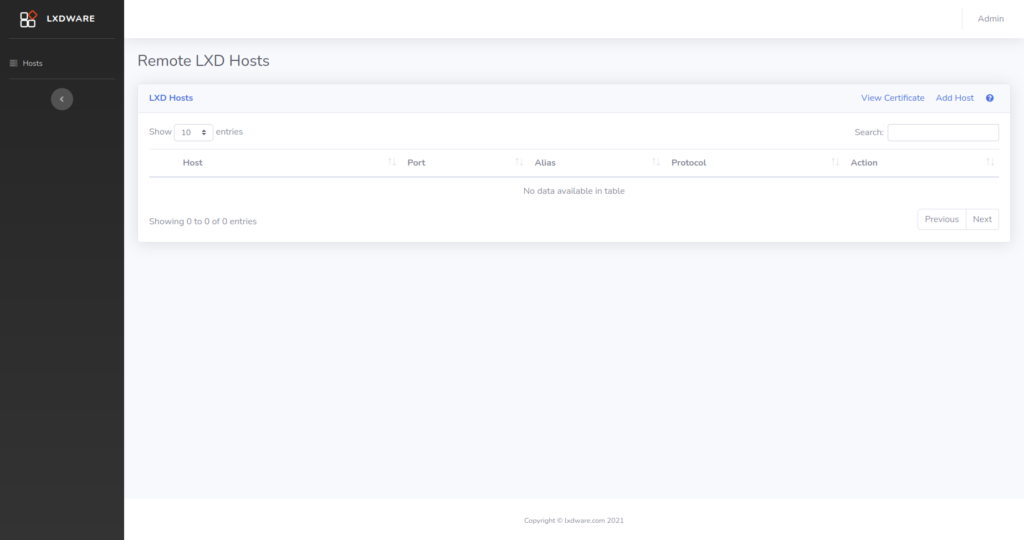
Initial setup
When you first login to the LXD dashboard you will be redirected to the Remote LXD Hosts page. Here you can setup the parameters needed to connect to the LXD servers that you plan to manage.
Help instructions are available on the Remote LXD Hosts page and can be viewed by clicking the help icon located at the top right of the table.
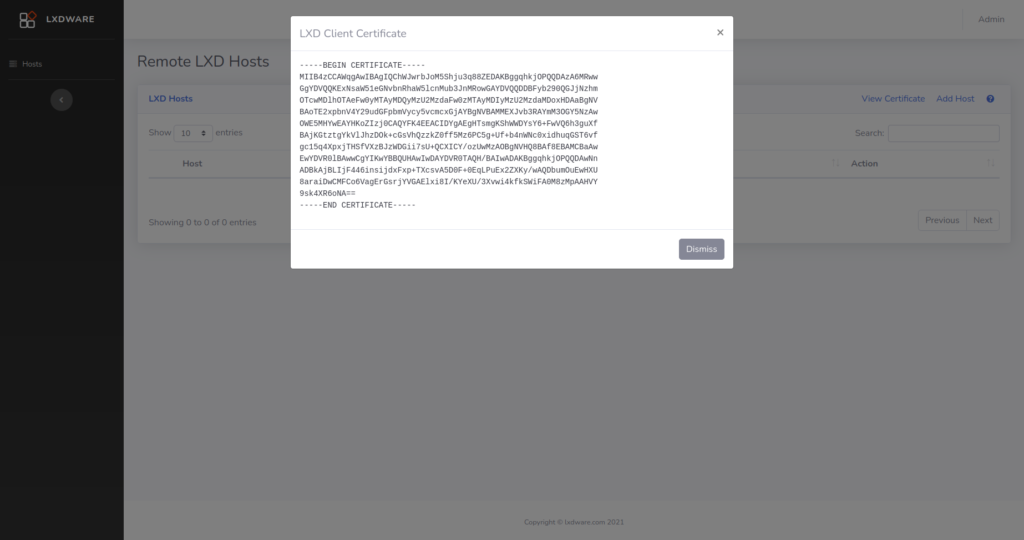
Client Certificate
A client certificate is generated when you first setup the LXD dashboard and is used to securely connect to your LXD servers. Click the View Certificate link to display the certificate. Copy and paste the certificate information into a new file on your LXD server named lxdware.crt.
Import the certificate by running the lxc config trust add lxdware.crt command on your server. If your server was not setup to listen for incoming connections run the lxc config set core.https_address [::] command.
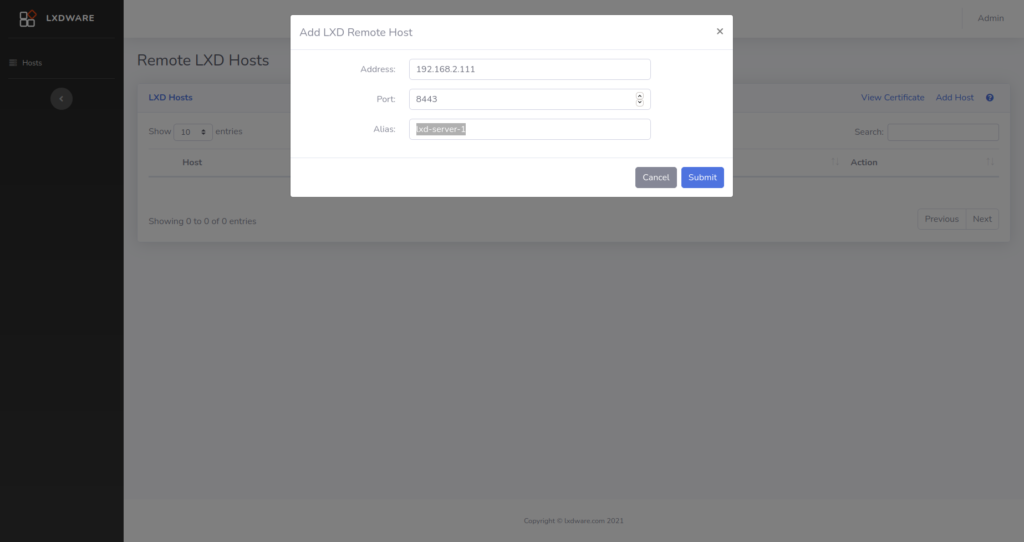
Adding your LXD Server
Now that your LXD server is listening for remote connections and trusts the LXD dasbhoard certificate it is time to add in the connection details of your LXD server. Click the Add Host link to display an entry form.
The Address field can be either an IP address or FQDN of your server. LXD uses port 8443 by default to connect remotely to hosts, however the Port field can be changed for your environment. The Alias field is just a friendly string to quickly identify and differentiate your server.
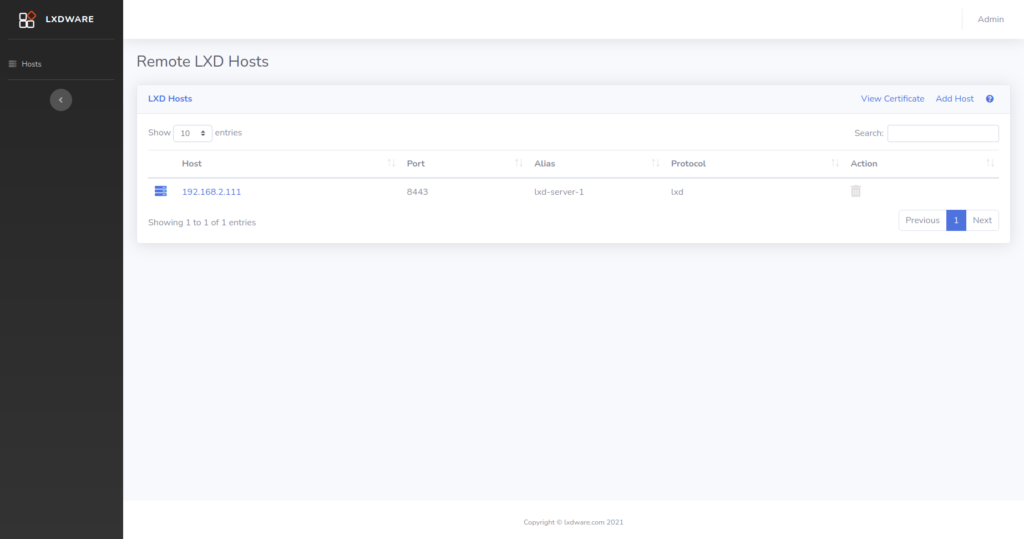
Hosts Table
Once your host has been added to the table, click the link provided in the Host column to start managing your LXD server. You are not limited to the number of hosts you wish to add.
Removing hosts can be completed by clicking on the delete icon in the table. This will remove your host connection information from the LXD dashboard database. If you are removing a host be sure to also remove the client certificate from your LXD server.

Hi Matthew,
I have an issue with adding my host to the dashboard. lxd-dashboard runs on a macvlan profile, so I am not sure if this is the issue. The dashboard reports `Error: Unable to connect to host` when I attempt to add my host. The certificate has been imported on the host.
Can you please advise?
Thank you.
Radu. So that error occurs when the REST API on your server does not return back the {“auth”:”trusted”} value. So I am thinking one of two issues. One being that you can’t connect to the server through the network or two the certificate is not loaded correctly. To test the first, login to the instance running the dashboard and try connecting use curl on the command line to the server. For example:
curl -k -L -X GET "https://192.168.2.100:8443/1.0". This should return untrusted data. To test for the second problem try using the certificate/key to see if it returns back trusted data. For example:curl -k -L --cert "/var/lxdware/data/lxd/client.crt" --key "/var/lxdware/data/lxd/client.key" -X GET "https://192.168.2.100:8443/1.0/instances. This should tell you which problem you are having.Version 2.0.0 now differentiates between these two issues, offing two different error messages depending on whether the error is a certificate error or connection error.
Thank you. I’ve installed v2.0 using default bridge and it works like a charm.
Great! Glad to hear it.
Matthew, please accept my apologies for hijacking your blog post. I was searching online for a Web interface for clamav but I cannot find anything suitable. I was wondering if you would consider a separate LXDWare project to build an “End Point ATP” dashboard where clamav is the agent running on the instances. Perhaps in the future other agents/modules (rkhunter) can be introduced for a complete open source security solution. Thanks again for your excellent work. Kind regards, Radu
That is no problem Radu. I need to get around to creating a forum or a page for suggestions for LXDWARE. ClamAV may actually be something I will work on in the near future. I am creating another open source dashboard project for controlling postfix/dovecot mail servers. ClamAV is often used in these setups, so I may include that in the project. If not in that project, then I may consider it in a separate project itself. Thanks for the suggestion.
Hi,
Just after finishing installation and first web logon, the View Certificate buttom shows no certificate (blank). What can I do to resolve this?
Thanks
It could be that web server (www-data) doesn’t have write capabilities to create the certificate. On your host operating system this should be located at your [mount location]/lxdware/data/lxd/ if you are using docker, or if you are running it in your own Linux server it would be the /var/lxdware/data/lxd/
directory. Once write permissions are available a new certificate should be created automatically when viewing the certificate in the dashboard.